Threats are continuously changing, and the cybersecurity environment is also evolving. Stakes are high in the banking and financial sector because large sums of money are at risk, and there is a chance that banks and other financial systems will be compromised, which could cause significant economic disruption.
New opportunities, however, bring with them new risks, particularly those related to cyber security. Financial services have the highest cost of all the industries analyzed for cybercrime, according to a report by Accenture. Consider one of the biggest data breaches in recent memory, the Equifax incident in 2017, which resulted in the exposure of 147 million people’s personal data. Following the incident, Equifax has spent $1.4 billion just on security upgrades. Of course, that doesn’t include the restitution given to individuals whose data was compromised, legal fees, and numerous other expenses.
The National Institute of Standards and Technology (NIST) is a government agency in the United States of America that provides guidelines and best practices for cybersecurity. The NIST Cybersecurity Framework (CSF) is a widely recognized and widely used set of guidelines that organizations can use to manage and reduce cybersecurity risk.
Here are the steps to apply NIST principles to strengthen your cybersecurity posture:
- Identify and prioritize assets:
Identify the most critical assets in your organization, including hardware, software, data, and personnel. Prioritize them based on their importance to your business operations and the potential impact if they were compromised.
- Assess risk:
Conduct a risk assessment to determine the likelihood and potential impact of different types of cybersecurity threats. Use the NIST CSF to help you identify and prioritize risks.
- Develop a risk management plan:
Develop a plan to mitigate identified risks. This plan should include specific actions to reduce or eliminate the risk, as well as measures to detect and respond to potential security incidents.
- Implement security controls:
Implement security controls to reduce the risk of cyber-attacks. This can include measures such as firewalls, intrusion detection systems, and antivirus software.
- Monitor and review:
Regularly monitor and review your cybersecurity posture to ensure that your security controls are working effectively. Use metrics to track your progress and identify areas for improvement
- Improve and adapt:
Continuously improve and adapt your cybersecurity posture based on new threats and changes to your business operations. Use the NIST CSF to help you stay up-to-date with the latest best practices.
What Is NIST Cybersecurity Framework (CSF)
The National Institute of Standards and Technology (NIST) has developed a set of guidelines called the NIST Cybersecurity Framework (CSF) to assist organizations in managing and lowering cybersecurity risk. It was created in response to Executive Order 13636, which called for the creation of a voluntary framework for enhancing cybersecurity throughout critical infrastructure sectors.
The NIST CSF is divided into three sections: Framework Core, Framework Profile, and Framework Implementation Tiers.
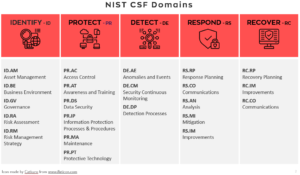
The Framework Core is a set of cybersecurity activities, outcomes, and informative references organized into five categories: identity, protection, detection, response, and recovery. These categories help organizations manage and reduce cybersecurity risk by identifying, protecting against, detecting, responding to, and recovering from cybersecurity threats.
The Framework Profile is a customized set of cybersecurity activities and outcomes that an organization selects based on its business needs, risk management strategy, and other factors.
The Framework Implementation tiers provide a way for organizations to evaluate their current cybersecurity capabilities and develop a roadmap for improving their cybersecurity posture.
Overall, the NIST CSF provides a flexible and scalable framework that can be used by organizations of all sizes and across all industries to manage and reduce cybersecurity risk. It is widely used and recognized as a best practice for cybersecurity management.